Cranbrook Managed IT Services Company
Supercharge Productivity With Our IT Services in Cranbrook, BC
Meet all your technology needs – scaling, management, updating, PC repairs and services – with one of the most trusted managed services providers in Cranbrook area.
Why choose Sunco for managed IT services in Cranbrook?
- Leverage end-to-end IT services and solutions with a partner that has over 20 years of experience in the industry.
- Cut IT costs and get the most out of your tech budget with our custom services and transparent invoicing.
- Work with proven IT specialists who are subject matter experts in all things IT and communication.
- Get the help you need when you need it with Cranbrook managed services teams that respond to issues within 2 hours.
Solve all your IT issues – no matter what it takes. Even if it means getting our CEO involved, we’ll fix your IT problems.
Trusted by 1,600+ Customers Across Canada
Request a quote for managed IT services in Cranbrook, British Columbia
Minimize downtime, maximize uptime with an Cranbrook-based team that understands your priorities.
Sunco Communication and Installation Ltd.
Cranbrook Managed IT Services
20 11 Ave S
Cranbrook, BC
V1C 2P1, Canada
Request a Quote:
250-426-1037
Leading Managed IT Services in Cranbrook

Managed IT Services
Get day-to-day support and management for all your technology from experts. We support businesses with 10-500 seats.

IT Consulting
Growing your business is easier with technology intelligence and insight that allows your business to develop free from tech constraints.

Cybersecurity
Protect your business with real-time alerts and security awareness training so all vulnerabilities are closed.

Cloud Services
Work with cutting-edge cloud solutions provided by a team that supports private, public, and hybrid cloud setups.

IT Support Services
Let us manage your projects, resolve recurring issues, and procure hardware and software upgrades at industry-insider prices.

Network Management
Work with a dependable, secure network with 24/7 network monitoring. Our team will architect and manage all your IT networks.

IT Helpdesk
No matter what IT issue you face, we’ll help you get it fixed. We’re never more than an email or phone call away.

Disaster Recovery
Ensuring business continuity with disaster recovery and backup planning. No matter what scenario occurs, be prepared.

Business Communication
Install and upgrade to the latest business phone technology, with terms from providers and industry-insider rates.

PC Repair and Services
Get complete repair and overhaul services from experienced technicians for your PCs and laptops of all makes and models.
What Makes Sunco Special

20+ Years
Providing Cranbrook IT solutions and services

1,600+
Customers supported Canada-wide

15%
Cost savings on average for our customers
Fully Managed IT Services in Cranbrook

Meet All Your IT Demands With a Single MSP Provider
Work with a Cranbrook managed services provider that helps you achieve your business goals faster with the help of leading technical services.
With Sunco, you can:
- Eliminate IT issues
- Lower costs
- Scale seamlessly
- Boost productivity across the company
Offload your day-to-day IT management so you can get back to focusing on your business.

Ironclad Cybersecurity
We ensure that your IT stack is fully protected from cybersecurity attacks.
Upgrade your defenses with:
- Company-wide security planning and strategy
- Real-time threat detection and alerts (SIEM)
- Reliable security solutions
- Routine security awareness training
We’ll identify your vulnerabilities and close them, meet compliance standards, and reduce the overall risk of data breaches with fully tailored cybersecurity solutions.

Support Both On-Site and Remote
No matter where your IT issue occurs, we’ll be there to solve it.
Our real-time alerts allow us to assign the appropriate IT specialists to begin solving issues immediately, ensuring the cost to your business is minimized.
Benefit from responsive support-we respond to issues in less than 2 hours.

An Entire Team of Experts on Your Side
We aren’t like other managed IT services providers in Cranbrook that struggle to meet SLA minimums-we pride ourselves on going above and beyond.
You’ll never receive anything less than professional, personable service from a team of professional IT engineers who know and understand your technology – and your needs.
Even if it means getting our CEO involved, we’ll do whatever it takes to ensure your technology is running optimally.
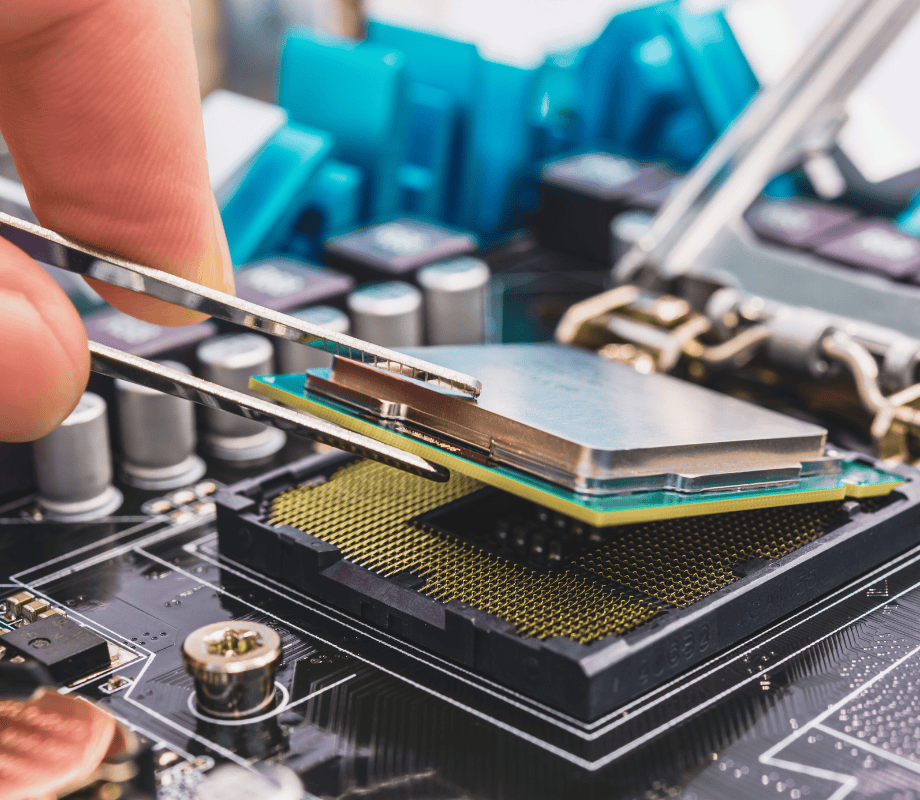
Revive your devices with unmatched PC and laptop repair expertise
Our skilled technicians have extensive experience diagnosing and fixing issues across all makes and models. From hardware repairs to software troubleshooting, we ensure your devices are restored to optimal performance.
You can trust us for reliable advice and efficient repair solutions tailored to your needs.

Sunco's Game-Changing Acquisition: Transforming IT Landscape in Cranbrook
Sunco Communication and Installation, a prominent industry leader, has strengthened its portfolio in East Kootenay by acquiring Isosceles Business Systems Inc. Isosceles, a renowned IT firm, was widely recognized for its exceptional expertise in managed IT services and consulting. This strategic acquisition further enhances Sunco’s position as a top-tier company in the field. This synergy streamlined services and enhanced local IT support. A strategic move, marking a turning point, benefiting clients and solidifying Cranbrook’s IT landscape.